Grokking Event-Driven Architectures: A Primer for Serverless Developers
Master the basics of event-driven systems. Learn how isolated publishers, independent subscribers, and central message brokers work together perfectly.
Software systems often begin as simple structures running on a single server.
As engineering teams add more features, the codebase becomes increasingly complex and difficult to maintain.
To manage this complexity, teams usually split the codebase into smaller independent services. These isolated services must constantly communicate over the network to function correctly.
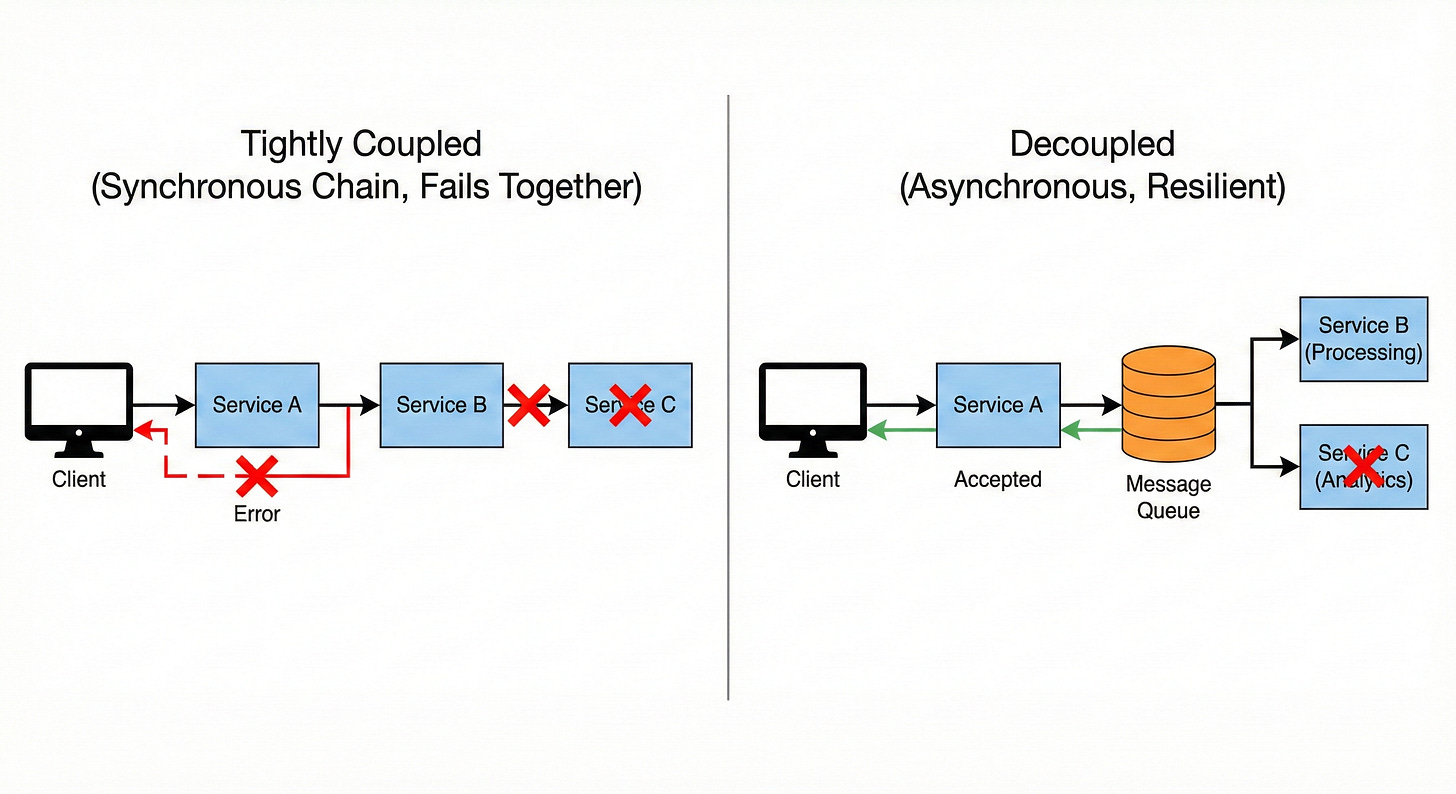
However, a massive problem emerges when these services communicate using direct, synchronous network requests.
Component A sends a request to Component B and completely halts all internal operations.
Component A sits idle and waits until Component B finishes computing and sends a response.
If Component B is slow or unresponsive, Component A is entirely blocked.
This waiting period creates a severe performance bottleneck across the entire software ecosystem.
One failing database query can trigger a chain reaction that takes the whole application offline. Tightly coupled architectures require enormous operational effort to scale and maintain under heavy traffic loads.
Understanding how to break these rigid dependencies is absolutely critical for modern system design.
What is Event-Driven Architecture?
Event-driven architecture changes the fundamental way software services interact with each other.
Instead of services giving direct commands and waiting for responses, they simply broadcast announcements. These internal system announcements state that a specific state change has occurred.
These data announcements are called events.
An event is just a tiny package of data containing facts about something that already happened.
For instance, a new data record gets inserted into a primary database. The database service generates an event containing the new data identification number and a creation timestamp. The system does not send this data to a predefined destination.
This paradigm shifts the software from a command-based model to a reactive model.
Components no longer instruct other components on what actions to perform. They simply observe the network environment and react when they detect an event they care about. This completely removes the tight coupling that plagues traditional synchronous systems.
Because an event describes a past action, it is completely immutable.
Immutability means the event data can never be altered or deleted by another service. It serves as a permanent historical record of a specific software action.
This strict factual record prevents accidental data corruption across the distributed system.
Breaking Down Publish and Subscribe
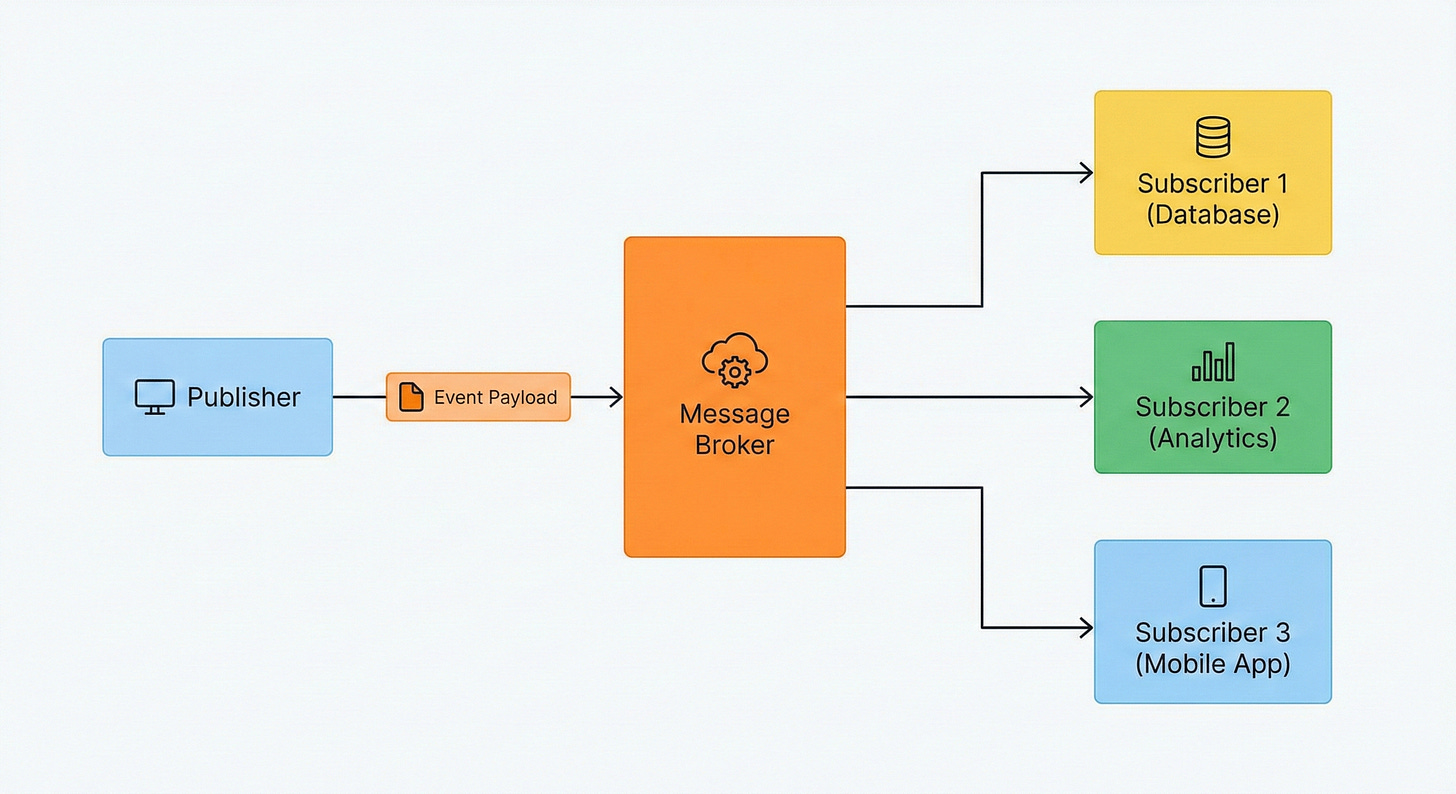
The most common way engineers implement event-driven communication is through a publish and subscribe model. Software developers often shorten this terminology to pub/sub.
This model securely separates the sender of a message from the eventual receivers.
The sender and the receivers operate entirely independently and do not know about each other.
The Event Publisher
A publisher is any software service or application component that generates an event. Its only responsibility is to format the event data and push it outward.
Once the event leaves the publisher, the publisher immediately moves on to its next computational task. It never waits for a confirmation from the final destination.
The publisher does not verify if the event was successfully processed by other backend services.
This fire-and-forget mechanism frees up memory and compute resources instantly.
The publisher remains highly responsive even under massive traffic loads. This is the core reason why decoupled systems perform so well.
The Message Broker
The central router in a pub/sub architecture is called a message broker.
Publishers transmit their events to specific logical categories within the broker. These logical categories are universally referred to as topics.
The broker acts as an incredibly fast temporary distribution center for the incoming data.
When an event lands in a topic, the message broker instantly duplicates the data. It then pushes the duplicated data out to interested listening parties.
The broker handles all the complex network routing logic internally.
This prevents the publisher from needing to manage a list of active network addresses.
The Event Subscriber
Subscribers are independent software applications that listen to specific topics hosted on the message broker.
When a new event arrives in a subscribed topic, the broker actively pushes a copy to the subscriber. A single published event might trigger ten different subscribers simultaneously.
The broker ensures each subscriber gets the exact same information.
Each subscriber processes the identical event data independently at its own computational pace.
A database service might subscribe to the topic to update search indexes.
A completely separate analytics service might subscribe to the exact same topic to generate reports.
If the analytics service crashes, the database service continues functioning without any interruption.
Securing the Message Broker
Security is another crucial aspect of managing an event-driven architecture. Because the message broker acts as the central hub for all system data, it must be fiercely protected.
Publishers and subscribers cannot simply connect to the broker without proving their identity. They must undergo strict authentication processes.
Before a publisher can send an event to a topic, it provides cryptographic credentials to the broker. The broker verifies these credentials against a secure internal database.
If the credentials are valid, the broker opens a dedicated connection for the data transfer.
This prevents malicious software from flooding the system with fake data payloads.
Subscribers face the exact same security requirements before they can listen to a topic.
The broker ensures that only authorized services can read sensitive system data.
This strict access control mechanism guarantees that the asynchronous data flow remains entirely private and secure.
Handling Message Failures
In asynchronous systems, software errors happen entirely out of sight.
A subscriber might receive an event but fail to process it due to a database lock. If the subscriber simply drops the data, the system loses valuable information.
To prevent data loss, engineers utilize dead letter queues.
Keep reading with a 7-day free trial
Subscribe to System Design Nuggets to keep reading this post and get 7 days of free access to the full post archives.