Leader-Follower Architecture: Designing for High Availability
Don't lose data in your system design. Master the differences between Synchronous, Asynchronous, and Semi-Synchronous replication.
Computer hardware is reliable, but it is not invincible.
In a traditional architecture where all your data lives on a single server, physical failures are catastrophic. When the server dies, your application stops, and the data typically disappears forever.
The standard solution to this physical reality is replication.
We do not store data on just one machine. We store exact copies of it on two, three, or even more machines simultaneously. If one machine fails, another is ready to take over.
However, moving data from one computer to another takes time. It involves sending electrical signals across cables, passing through network switches, and writing to physical disks. This introduces a fundamental choice in system design.
Do we wait for the copy to be saved before we tell the user the job is done?
Or do we tell the user “success” immediately and save the copy in the background?
This decision determines your Replication Mode. It is the specific configuration that balances durability (keeping data safe) against latency (responding quickly).
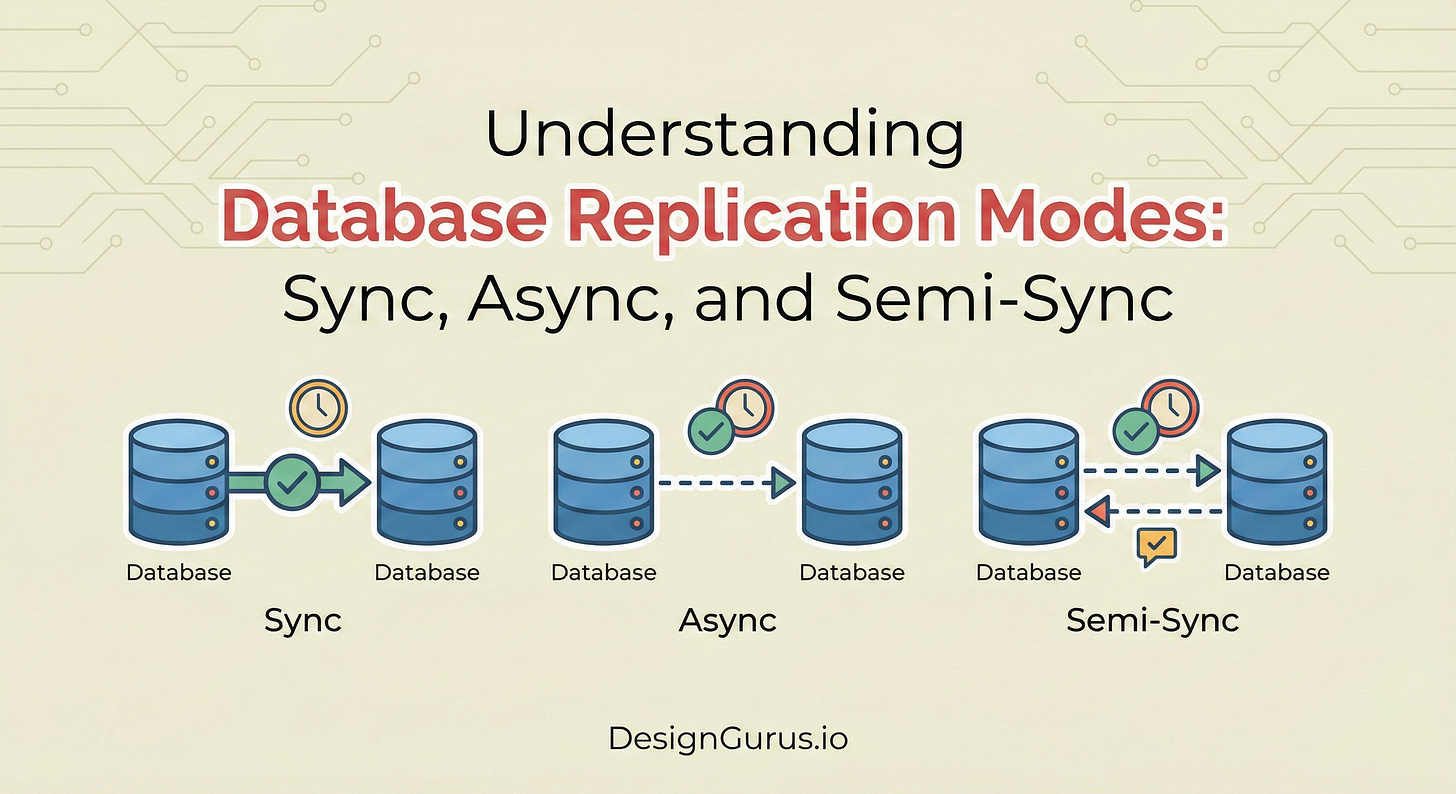
This guide explores the three main ways to handle this trade-off: Synchronous, Asynchronous, and Semi-Synchronous replication. We will look at how they work, why they matter, and how to choose the right one.
The Core Concept: Leader and Follower
Before analyzing the modes, we must understand the basic setup of a distributed database. Most systems use a Leader-Follower topology (also known as Primary-Replica).
The Leader (Primary): This is the authoritative source. All new data “writes” (creates, updates, deletes) must go to the Leader first.
The Follower (Replica): This is the backup. It sits passively and receives updates from the Leader. Its goal is to maintain an identical copy of the Leader’s data.
The difference between the replication modes lies entirely in the conversation between the Leader and the Follower.
Specifically, it depends on when the Leader decides it is safe to confirm success to the application.
Keep reading with a 7-day free trial
Subscribe to System Design Nuggets to keep reading this post and get 7 days of free access to the full post archives.