The Rate Limiter: Why This Classic Interview Question Derails Seniors
Master the rate limiter system design question. We explain the fixed window, sliding window, and token bucket algorithms for distributed architectures.
This blog will cover:
Protect servers from traffic.
Understand simple counting algorithms.
Scale across distributed servers.
Fix dangerous race conditions.
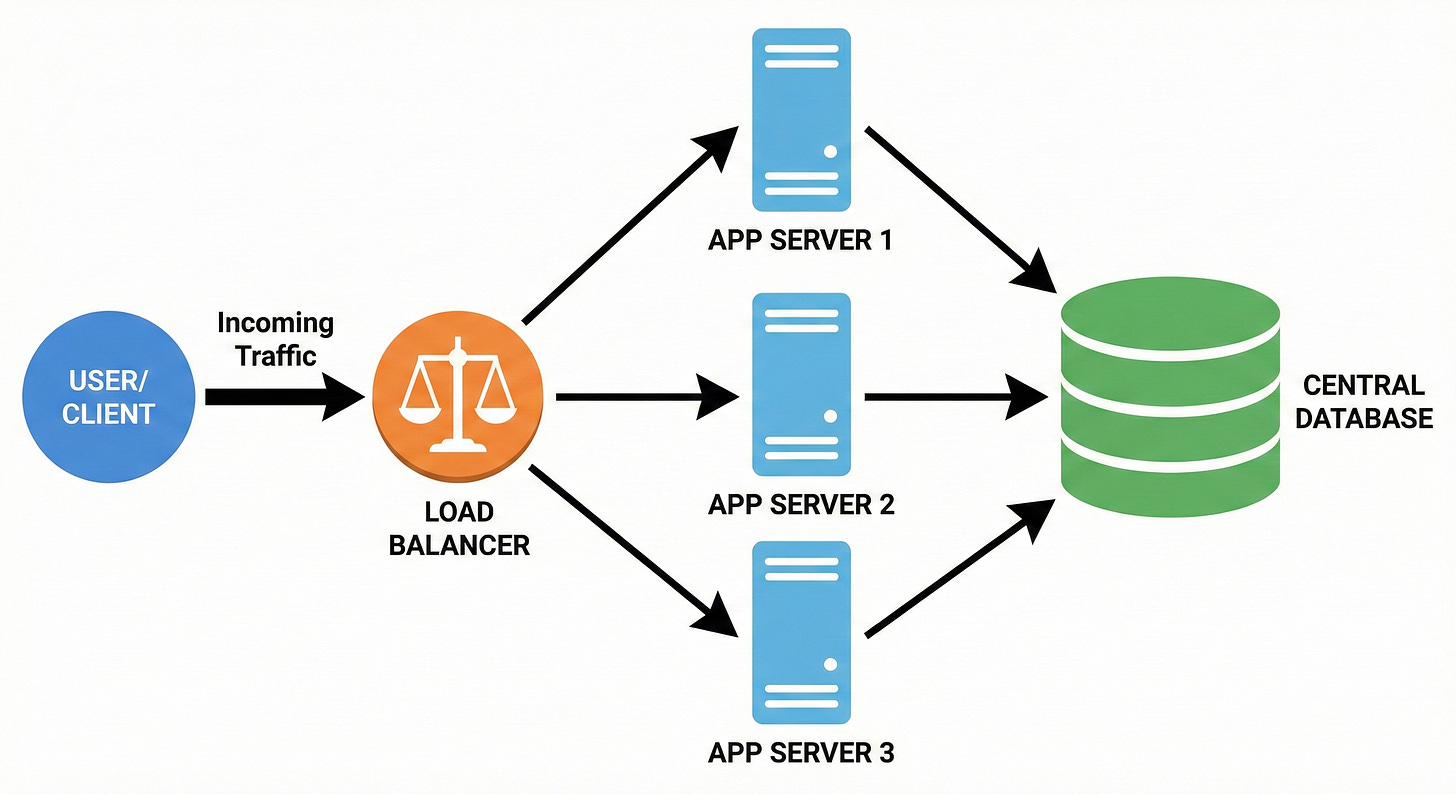
Hardware limits are a strict reality in software engineering. Every physical server has a finite amount of processing power and memory.
When incoming network traffic exceeds these strict physical boundaries, the software application begins to fail.
The server slows down drastically until it eventually crashes completely.
This hardware failure drops all active database connections and rejects legitimate network traffic. A sudden influx of automated network requests will consume all available system resources in seconds.
Engineering teams implement a specific defensive layer to prevent this systemic software collapse. This protective mechanism strictly controls the volume of incoming traffic.
This component is universally known as the rate limiter. It is a mandatory architectural pattern for any application handling public network traffic.
Understanding this concept is critical for building stable backend infrastructure.
Understanding the Rate Limiter
A rate limiter controls how many times a specific identity can trigger an action within a specific timeframe. It acts as a strict mathematical boundary for incoming network requests. The system tracks the exact number of requests coming from a unique digital identity.
This identity is usually an IP address, which is a unique string of numbers tied to a network connection.
If an application allows one hundred requests per minute, the rate limiter tracks the count. When a script sends the one hundred and first request, the system actively blocks it. The server returns a specific error code to the sender.
This code informs the sending software that it is transmitting data too quickly.
The sending software must pause its operations before trying again.
This simple blocking mechanism protects the core application from complete failure. Developers usually feel very confident when asked to build this system. Writing a basic script to count incoming requests is fundamentally simple.
The core logic only requires a few basic variables to track numbers and time. However, this simplicity is extremely deceptive.
The concept completely transforms when deployed in a massive enterprise architecture. Large applications introduce severe complexities that cause experienced developers to fail during technical interviews.
Basic Mathematical Filtering
Before looking at complex distributed failures, we must understand the basic mathematical approaches.
Developers rely on several distinct algorithms to calculate traffic limits. Each algorithm handles incoming network traffic differently.
The Fixed Window Approach
The fixed window algorithm divides time into rigid and predefined blocks.
A system might use blocks of exactly one minute. Each time block possesses its own dedicated counter variable.
When a network request arrives, the system checks the current time block. It increments the counter for that specific minute.
If the counter exceeds the maximum allowed number, the request is rejected.
When the minute ends, a completely new block begins with a counter of zero.
This approach requires very little system memory to operate. However, it suffers from a significant mathematical flaw at the edges of the time blocks.
A script could send a massive spike of traffic at the very end of one minute. It could then send another massive spike at the beginning of the next minute.
Both spikes are technically valid within their own separate time blocks. However, the system just allowed double the expected traffic within a few seconds.
This sudden volume can still overload the underlying application server.
The Sliding Window Log
The sliding window log resolves the mathematical flaw of the fixed window.
Instead of counting numbers in static blocks, this method tracks the exact timestamp of every single request. The system stores these timestamps in a sequential digital list.
Keep reading with a 7-day free trial
Subscribe to System Design Nuggets to keep reading this post and get 7 days of free access to the full post archives.