System Design Interview: How HTTPS and TLS Actually Work
Master HTTPS and TLS for your system design interview. Learn the exact steps of the TLS handshake, the difference between symmetric and asymmetric encryption.
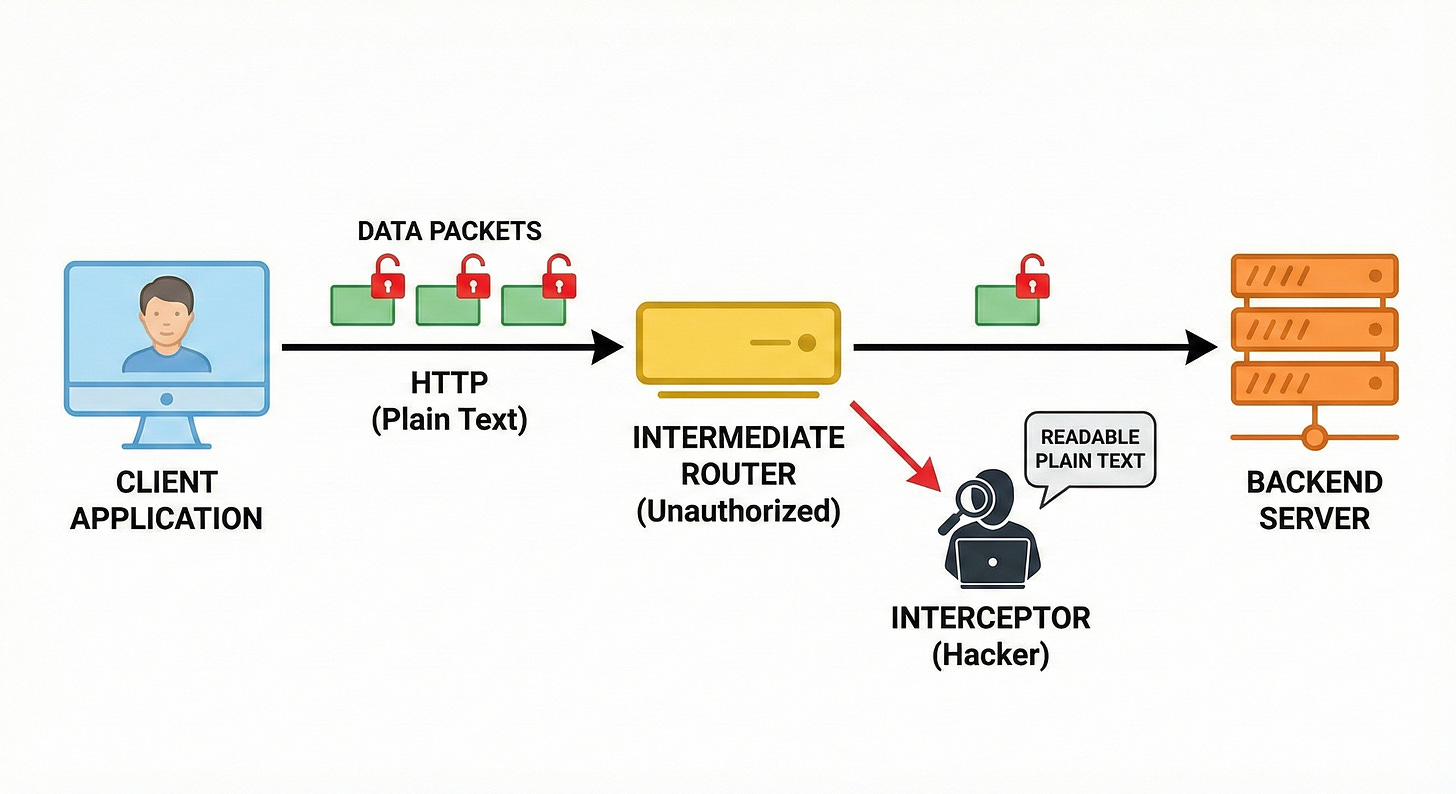
Every day, massive volumes of sensitive information travel across the global internet. This data must pass through dozens of independent routing devices before reaching a final destination.
Because the Internet's underlying infrastructure is fundamentally open, any intermediate routing device can silently inspect transmitted data packets.
If software applications transmit data without mathematical protection, malicious actors can easily capture passwords and authentication tokens.
Solving this critical security vulnerability is a mandatory requirement for modern system architecture.
Understanding the exact cryptographic mechanisms that protect network data is essential for building reliable software.
Engineers must implement specific protocols to guarantee that intercepted data remains completely unreadable to unauthorized parties.
The Vulnerability of Plain Text Data
To understand why network security is so important, we must examine the default behavior of internet communication.
The foundational technology for web communication is the Hypertext Transfer Protocol, commonly known as HTTP.
Standard HTTP strictly defines how web clients and servers format their messages. However, standard HTTP lacks any built in mechanism for data encryption.
When an application uses standard HTTP, all data is transmitted exactly as it is formatted in plain text. If a client application sends a data payload containing a user password, those exact characters travel across the open network.
Network diagnostic tools can easily capture and read these raw data packets. Malicious actors actively use these packet sniffing techniques to silently record sensitive information without detection.
Furthermore, standard HTTP cannot mathematically verify data integrity during network transit.
An intercepting routing node can maliciously modify the data packet before forwarding it to the final destination server. The receiving server has absolutely no technical method to detect that the payload was altered.
To resolve these severe vulnerabilities, engineers introduced complex mathematical cryptography into the network stack.
The Evolution of Secure Network Protocols
To solve the interception problem, software engineers rely on mathematical encryption.
Keep reading with a 7-day free trial
Subscribe to System Design Nuggets to keep reading this post and get 7 days of free access to the full post archives.