JSON Web Tokens Explained: The Authentication Pattern Behind Every Modern API
Discover how data is securely transmitted between parties using the JWT standard. We break down the signing and verification process.
The evolution of software architecture has introduced significant challenges in how systems handle user data.
In the early days of the web, applications were typically hosted on a single server. This server handled everything from the user interface to the database connections.
When a user logged in, the server simply remembered them in its memory.
However, modern applications rarely live on a single machine.
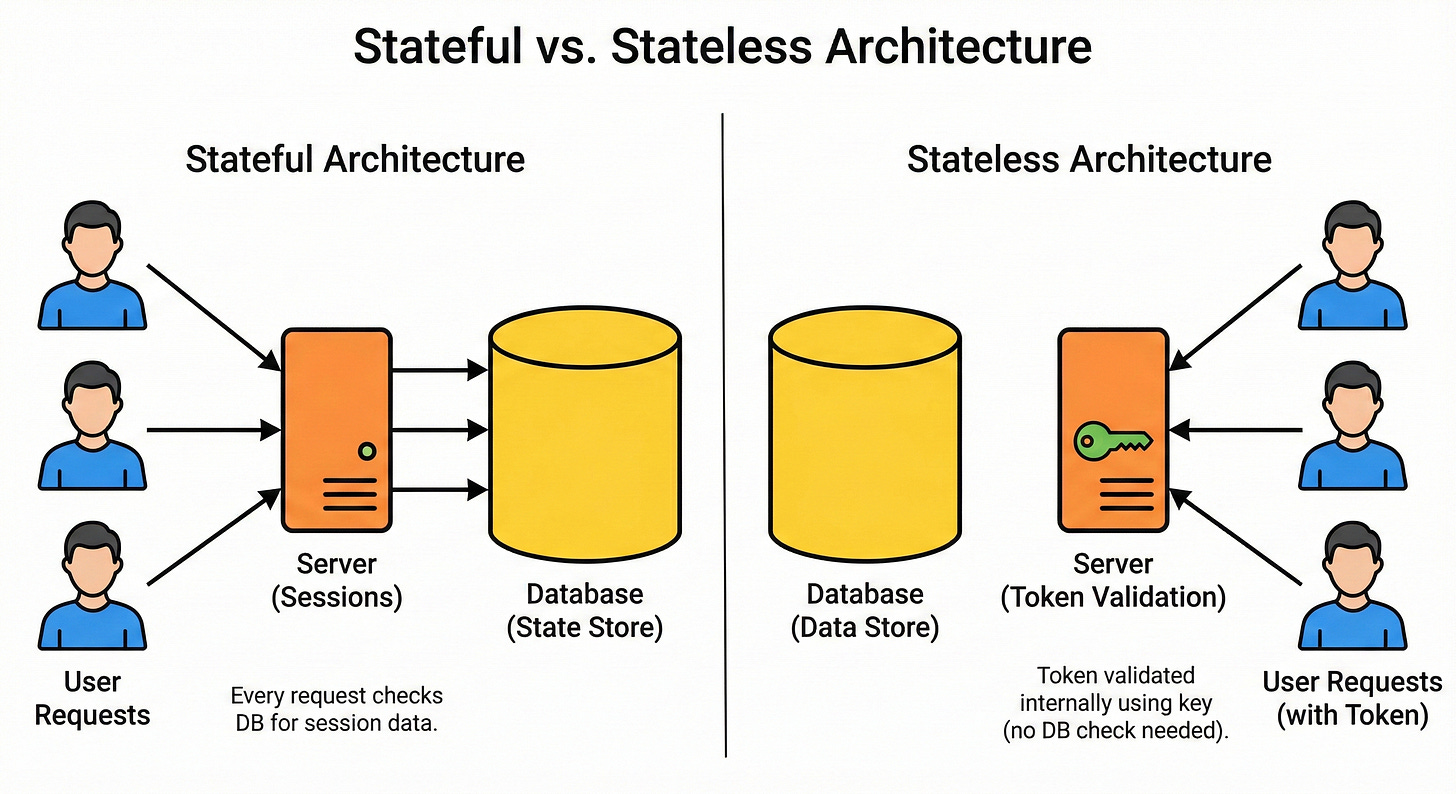
To handle millions of concurrent users, systems are distributed across hundreds of servers. This shift creates a fundamental engineering problem. If a user logs into one server, how does a different server know who they are without asking a central database every single time?
This is the core problem of state in distributed systems.
The industry solution to this challenge is a standard known as the JSON Web Token, or JWT.
Understanding this concept is critical for any developer working on modern APIs or preparing for system design interviews. It represents a move away from centralized session storage toward a portable, verifiable identity mechanism.
The Engineering Challenge: State vs. Scale
To understand why JWTs are necessary, we must look at the limitations of the traditional approach known as server-side sessions.
The web operates on HTTP, a protocol that is stateless by design.
This means the server treats every request as a brand new interaction. It has no memory of the request that came before it. To bridge this gap, developers traditionally used sessions.
When a user logged in, the server created a record in its memory. It assigned the user a Session ID.
For every subsequent click or request, the user’s browser sent this ID back to the server.
The server took the ID, looked it up in its memory, and confirmed the user’s identity.
This method hits a bottleneck as soon as the application scales.
Imagine an application running on a cluster of fifty servers.
A user’s request is routed to Server 1, where they log in.
Server 1 stores their session data. The user’s next request might be routed to Server 2 by a load balancer.
Server 2 has no record of this user. It rejects the request, forcing the user to log in again.
To fix this, engineers have to implement complex solutions. They might use “sticky sessions” to force a user to always visit the same server, which causes uneven traffic distribution.
Alternatively, they might set up a massive, shared database just for session data (like Redis). This introduces a single point of failure and adds network latency to every single API call.
This structural limitation created the need for a stateless authentication method.
The goal was to verify a user’s identity without the server needing to save any record of the login.
What is a JSON Web Token?
A JSON Web Token (RFC 7519) is an open standard that defines a compact and self-contained way for securely transmitting information between parties as a JSON object.
The most important term here is self-contained.
In a session-based world, the “proof” of identity is stored on the server.
In a token-based world, the proof is stored inside the token itself.
The token contains the user’s ID and permissions.
The server does not need to look up a database to find out who the user is; it simply reads the token.
Because the token contains data, it must be trusted.
Keep reading with a 7-day free trial
Subscribe to System Design Nuggets to keep reading this post and get 7 days of free access to the full post archives.