How to Secure and Scale Your App: A Guide to Nginx, Proxies, and LBs
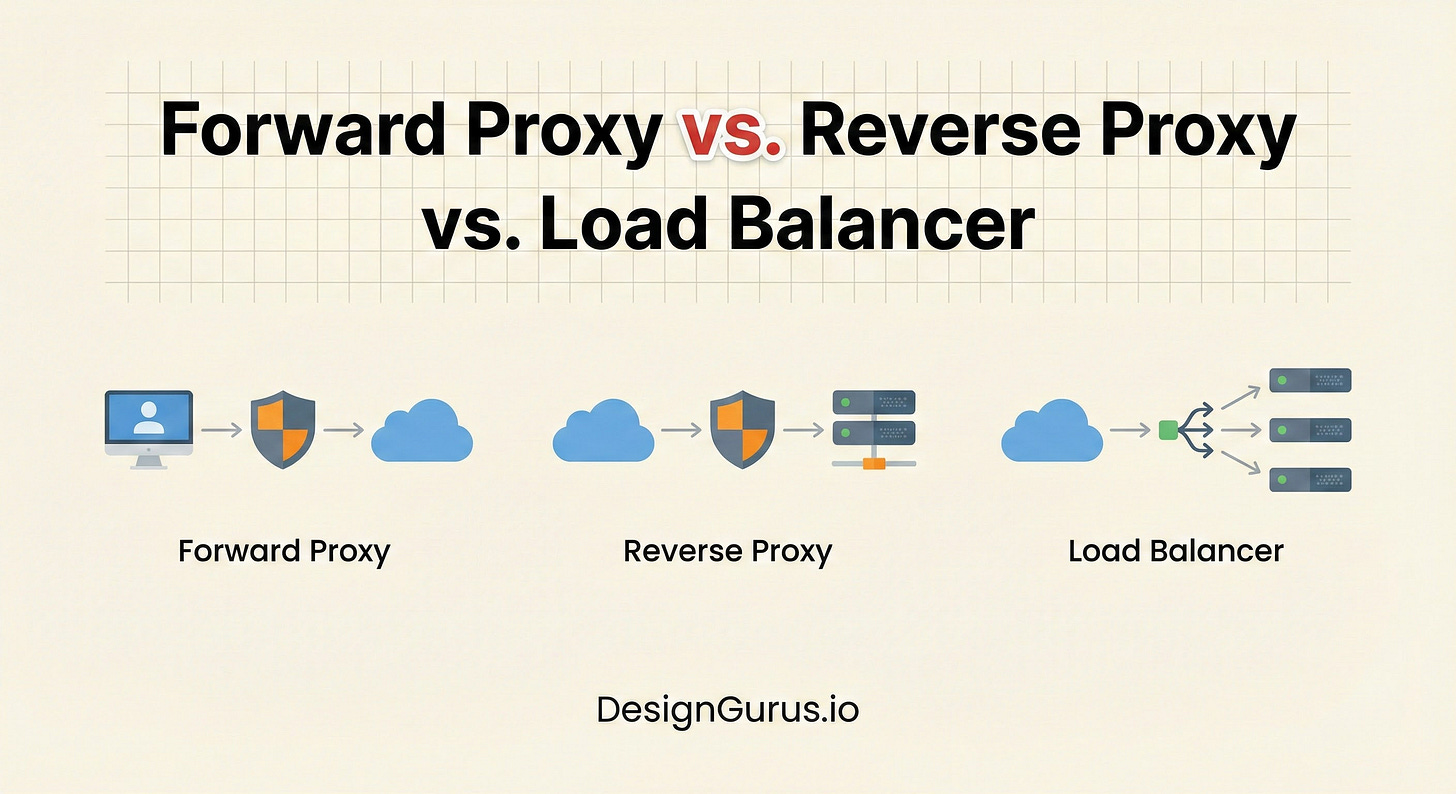
Stop confusing your proxies. Learn the exact difference between Forward Proxies (Client Anonymity), Reverse Proxies (Server Security), and Load Balancers (Scaling).
When you begin your journey into system design, you often start with a simple mental model.
You have a client (your computer) and a server (the machine running your code). You send a request, and the server sends a response. This direct connection works perfectly in a local development environment.
However, moving code into a production environment introduces complex challenges.
You must handle security threats, privacy concerns, and massive spikes in traffic.
A direct connection between a user and a database or application server is rarely secure or scalable enough for the real world.
To solve these problems, system architects introduce intermediaries. These are servers that sit between the client and the destination to manage the flow of data.
The three most critical intermediaries you need to understand are the Forward Proxy, the Reverse Proxy, and the Load Balancer.
This guide will break down the exact differences between these components. You will learn where they sit in the network, whose identity they protect, and how they function technically.
The Intermediary
Before we define the specific types, we must understand the general function of a proxy.
In computer networking, a proxy is a gateway.
It is a server that acts as a central point of contact. Instead of connecting directly to a destination, you connect to the proxy.
The proxy effectively speaks on your behalf. It takes your request, performs an action (like logging, filtering, or encrypting), and then forwards the request to the next stop in the chain.
The type of proxy is defined by who it is protecting and where it sits in the communication line.
1. The Forward Proxy: Protecting the Client
When people use the word “proxy” in a casual context, they are usually referring to a Forward Proxy.
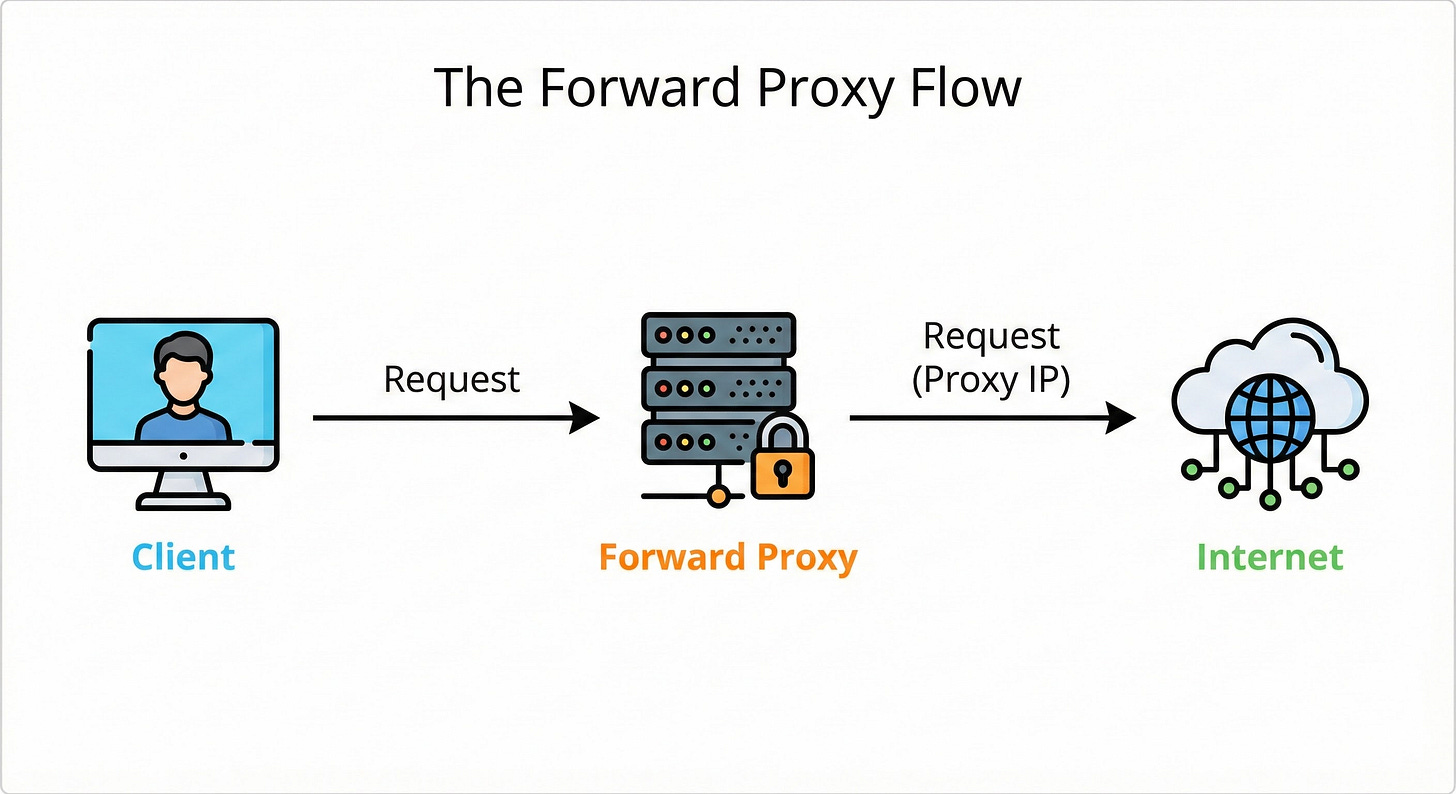
A Forward Proxy sits in front of the client. It acts as a representative for the user.
In this architecture, the client (User A) wants to access a server (Server B).
However, User A does not send the request directly to Server B.
Instead, User A sends the request to the Forward Proxy. The proxy intercepts the request and forwards it to Server B.
How It Works
The Request: The client sends a request intended for the internet to the Forward Proxy.
The Processing: The proxy inspects the request. It may check if the client has permission to access the destination.
The Forwarding: The proxy sends the request to the destination server on the internet.
The Response: The destination server sends the data back to the proxy.
The Delivery: The proxy sends the data back to the client.
Why Do We Use It?
The primary goal of a Forward Proxy is to act on behalf of the client. It provides privacy, control, and access.
Privacy and Anonymity (VPNs)
This is the most common use case for individuals.
When a Forward Proxy forwards a request, the destination server sees the IP address of the proxy, not the client.
The server has no idea who the actual originator of the request is. This masks the client’s identity. This is the fundamental technology behind a Virtual Private Network (VPN).
Content Filtering
In corporate environments or educational institutions, administrators use Forward Proxies to control outbound traffic.
All traffic from employees or students must pass through the proxy.
The proxy inspects the destination URL.
If the user is trying to access a blocked site (like social media or a gaming site), the proxy refuses to forward the request.
Bypassing Restrictions
This works in the opposite direction as well.
If a specific server blocks traffic from your country or region, you can connect to a Forward Proxy located in a different region.
The destination server sees the request coming from the proxy’s location (which is allowed) and grants access.
Key Takeaway: A Forward Proxy hides the Client from the Server.
2. The Reverse Proxy: Protecting the Server
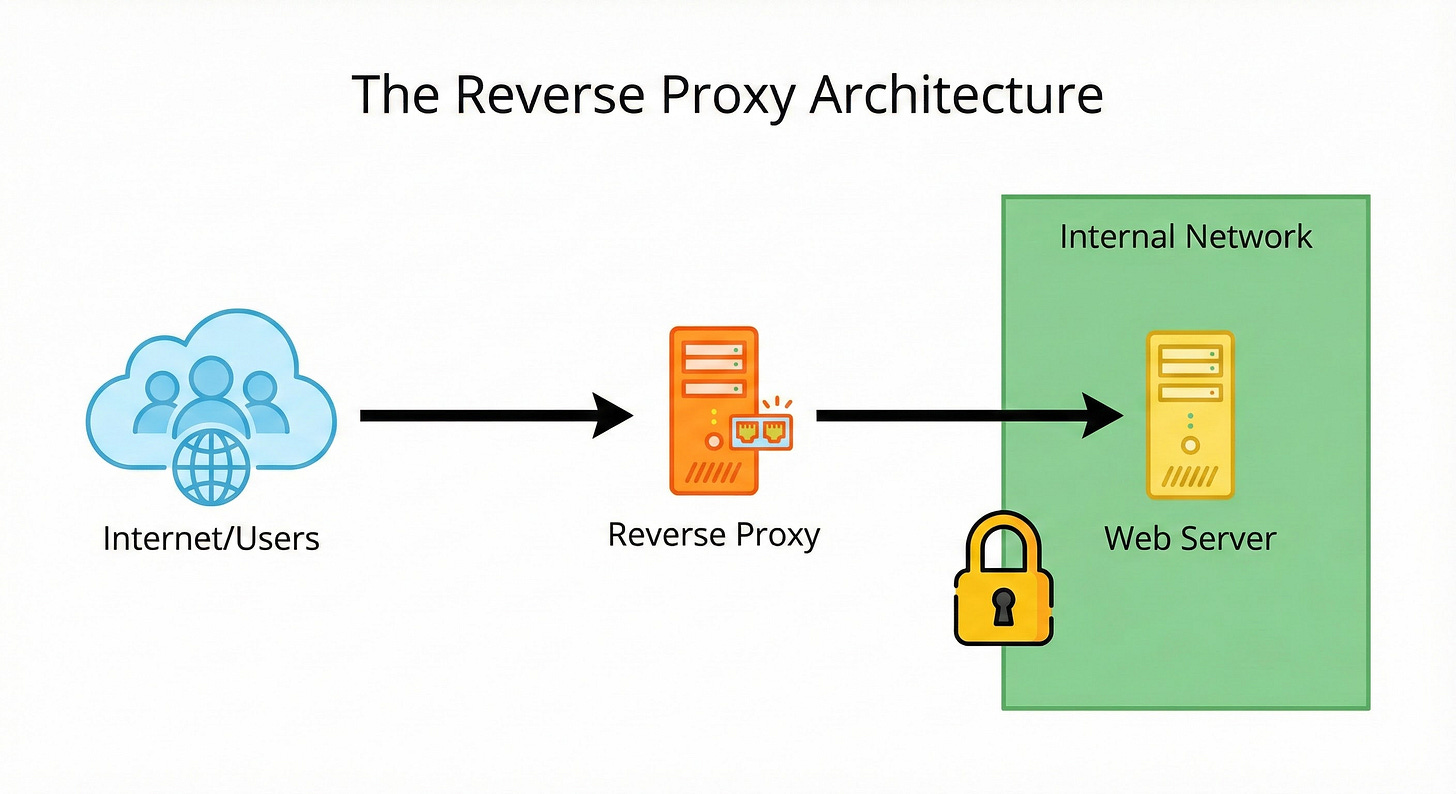
A Reverse Proxy is the architectural opposite of a Forward Proxy.
While the Forward Proxy sits in front of the client, the Reverse Proxy sits in front of the server.
From the client’s perspective, the Reverse Proxy is the web server. The user types in a domain name, and their browser connects to an IP address. They believe they are communicating directly with the application.
In reality, they are connecting to the Reverse Proxy. The Reverse Proxy accepts the connection, determines which internal server should handle the request, and retrieves the data.
How It Works
The Connection: A client sends a request to a website’s public IP address.
The Interception: This IP belongs to the Reverse Proxy. It accepts the request.
The Routing: The proxy looks at the request and forwards it to a specific backend server located on a private internal network.
The Retrieval: The backend server processes the logic and returns the response to the proxy.
The Response: The proxy delivers the data to the client.